
Q . I COMPUTER WORM
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers.[1] Often, it uses a computer network to spread itself, relying on security failures on the target computer to access it. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer.
Many worms that have been created are designed only to spread, and do not attempt to change the systems they pass through. However, as the Morris worm and Mydoom showed, even these "payload-free" worms can cause major disruption by increasing network traffic and other unintended effects
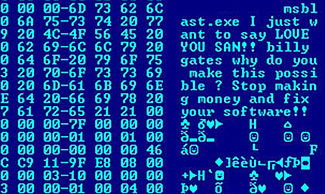
Hex dump of the Blaster worm, showing a message left for Microsoft CEO Bill Gates by the worm programmer
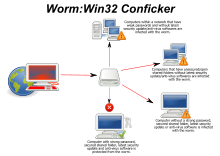
Spread of Conficker worm
The actual term "worm" was first used in John Brunner's 1975 novel, The Shockwave Rider. In that novel, Nichlas Haflinger designs and sets off a data-gathering worm in an act of revenge against the powerful men who run a national electronic information web that induces mass conformity. "You have the biggest-ever worm loose in the net, and it automatically sabotages any attempt to monitor it... There's never been a worm with that tough a head or that long a tail!"[2]
On November 2, 1988, Robert Tappan Morris, a Cornell University computer science graduate student, unleashed what became known as the Morris worm, disrupting a large number of computers then on the Internet, guessed at the time to be one tenth of all those connected[3] During the Morris appeal process, the U.S. Court of Appeals estimated the cost of removing the virus from each installation was in the range of $200–53,000, and prompting the formation of the CERT Coordination Center[4] and Phage mailing list.[5] Morris himself became the first person tried and convicted under the 1986 Computer Fraud and Abuse Act.[6]
Harm
Any code designed to do more than spread the worm is typically referred to as the "payload". Typical malicious payloads might delete files on a host system (e.g., the ExploreZip worm), encrypt files in a ransomware attack, or exfiltrate data such as confidential documents or passwords.Probably the most common payload for worms is to install a backdoor. This allows the computer to be remotely controlled by the worm author as a "zombie". Networks of such machines are often referred to as botnets and are very commonly used for a range of malicious purposes, including sending spam or performing DoS attacks.
Countermeasures
Worms spread by exploiting vulnerabilities in operating systems. Vendors with security problems supply regular security updates[12] (see "Patch Tuesday"), and if these are installed to a machine then the majority of worms are unable to spread to it. If a vulnerability is disclosed before the security patch released by the vendor, a zero-day attack is possible.Users need to be wary of opening unexpected email,[13][14] and should not run attached files or programs, or visit web sites that are linked to such emails. However, as with the ILOVEYOU worm, and with the increased growth and efficiency of phishing attacks, it remains possible to trick the end-user into running malicious code.
Anti-virus and anti-spyware software are helpful, but must be kept up-to-date with new pattern files at least every few days. The use of a firewall is also recommended.
In the April–June 2008 issue of IEEE Transactions on Dependable and Secure Computing, computer scientists described a new and potentially effective way to combat internet worms. The researchers discovered how to contain worms that scanned the Internet randomly, looking for vulnerable hosts to infect. They found that the key was to use software to monitor the number of scans that machines on a network send out. When a machine started to send out too many scans, it was a sign that it has been infected, which allowed administrators to take it off line and check it for malware.[15][16] In addition, machine learning techniques can be used to detect new worms, by analyzing the behavior of the suspected computer.[17]
Users can minimize the threat posed by worms by keeping their computers' operating system and other software up to date, avoiding opening unrecognized or unexpected emails and running firewall and antivirus software.[18]
Mitigation techniques include:
- ACLs in routers and switches
- Packet-filters
- TCP Wrapper/ACL enabled network service daemons
- Nullroute
Worms with good intent
Beginning with the very first research into worms at Xerox PARC, there have been attempts to create useful worms. Those worms allowed testing by John Shoch and Jon Hupp of the Ethernet principles on their network of Xerox Alto computers. The Nachi family of worms tried to download and install patches from Microsoft's website to fix vulnerabilities in the host system—by exploiting those same vulnerabilities.[19] In practice, although this may have made these systems more secure, it generated considerable network traffic, rebooted the machine in the course of patching it, and did its work without the consent of the computer's owner or user. Regardless of their payload or their writers' intentions, most security experts regard all worms as malware.Several worms, like XSS worms, have been written to research how worms spread. For example, the effects of changes in social activity or user behavior. One study proposed what seems to be the first computer worm that operates on the second layer of the OSI model (Data link Layer), it utilizes topology information such as Content-addressable memory (CAM) tables and Spanning Tree information stored in switches to propagate and probe for vulnerable nodes until the enterprise network is covered.
 Morris worm source code floppy diskette at the Computer History Museum
Morris worm source code floppy diskette at the Computer History MuseumQ . II Write once read many (WORM)
Write once read many (WORM) describes a data storage device in which information, once written, cannot be modified. This write protection affords the assurance that the data cannot be tampered with once it is written to the device.
On ordinary (non-WORM) data storage devices, the number of times data can be modified is limited only by the lifespan of the device, as modification involves physical changes that may cause wear to the device. The "read many" aspect is unremarkable, as modern storage devices permit unlimited reading of data once written
WORM drives preceded the invention of the CD-R and DVD-R. An example was the IBM 3363.[1] These drives typically used a 12 in (30 cm) disk in a cartridge, with an ablative optical layer that could be written to only once, and were often used in places like libraries that needed to store large amounts of data. Interfaces to connect these to PCs also existed.
Punched cards and paper tape are obsolete WORM media. Although any unpunched area of the medium could be punched after the first write of the medium, doing so was virtually never useful. Read-only memory (ROM) is also a WORM medium. Such memory may contain the instructions to a computer to read the operating system from another storage device such as a hard disk. The non-technical end-user, however, cannot write the ROM even once, but considers it part of the unchangeable computing platform.
WORM was utilized for Broker-dealer records within the Financial Industry Regulatory Authority and the U.S. Securities and Exchange Commission.
Current WORM drives
The CD-R and DVD-R optical disks for computers are common WORM devices. On these disks, no region of the disk can be recorded a second time. However, these disks often use a file system based on ISO 9660 that permits additional files, and even revised versions of a file by the same name, to be recorded in a different region of the disk. To the user of the disk, the disk appears to allow additions and revisions until all the disk space is used.A version of the Secure Digital flash memory card exists in which the internal microprocessor does not allow rewrites of any block of the memory.
Multiple vendors beginning in the early 2000s developed Magnetic WORM devices. These archival grade storage devices utilize a variation of RAID and magnetic storage technologies to secure data from unauthorized alteration or modification at both the hardware and software levels. As the cost of magnetic (and solid state) storage has decreased, so has the cost for these archival storage technologies. These technologies are almost always integrated directly to a content/document management system that manages retention schedules and access controls, along with document level history.[2]
There are multiple vendors providing Magnetic Storage technologies including (but not limited to) NetApp,[3] EMC Centera,[4] KOM Networks,[5] and others. In 2013, GreenTec-USA, Inc. developed WORM hard disk drives in capacities of 3 TB and greater. Prevention of rewrite is done at the physical disk level and cannot be modified or overridden by the attached computer.
Research
In recent years there has been a renewed interest in WORM based on organic components, such as PEDOT:PSS or other polymers such as PVK[10] or PCz. Organic WORM devices, considered organic memory, could be used as memory elements for low-power RFID tags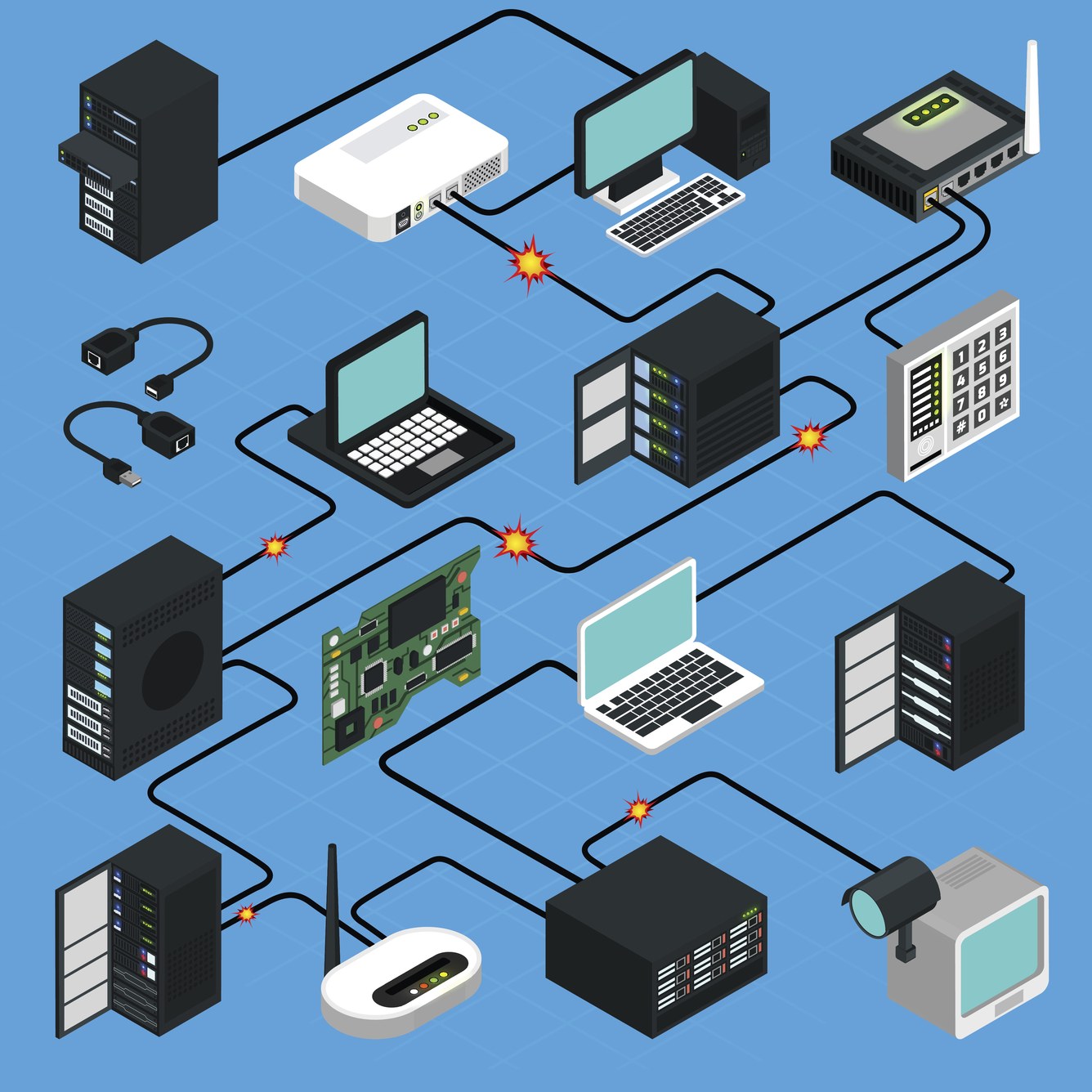
The Mirai worm is gnawing its way through the Internet of Things and will not stop
computer worm
A computer worm is a type of malicious software program whose primary function is to infect other computers while remaining active on infected systems
A computer worm is self-replicating malware that duplicates itself to spread to uninfected computers. Worms often use parts of an operating system that are automatic and invisible to the user. It is common for worms to be noticed only when their uncontrolled replication consumes system resources, slowing or halting other tasks.
A computer worm is not to be confused with WORM (write once, read many).
How computer worms spread
A computer worm infection spreads without user interaction. All that is necessary is for the computer worm to become active on an infected system. Before widespread use of networks, computer worms were spread through infected storage media, such as floppy diskettes, which, when mounted on a system, would infect other storage devices connected to the victim system. USB drives are still a common vector for computer worms.Computer worms often rely on the actions of, and vulnerabilities in, networking protocols to propagate. For example, the WannaCry ransomware worm exploited a vulnerability in the first version of the Server Message Block (SMBv1) resource sharing protocol implemented in the Windows operating system. Once active on a newly infected computer, the WannaCry malware initiates a network search for new potential victims: systems that respond to SMBv1 requests made by the worm. The worm is able to continue to propagate within an organization in this way. When a bring your own device is infected, the worm can spread to other networks.
Email worms spread by creating and sending outbound messages to all the addresses in a user's contacts list.
Stuxnet, one of the most notorious computer worms to date, consists of a worm component for propagation of the malware through the sharing of infected USB devices, as well as malware that targets supervisory control and data acquisition systems, which are widely used in industrial environments, including power utilities, water supply services, sewage plants and elsewhere.
Types of computer worms
Pure computer worms propagate themselves from infected systems to uninfected systems. This does not minimize the potential for damage from such computer worm .Common threats to be aware of
Learn about the latest online scams and what you should know to ensure safe Internet browsing.
Botnets
If you've never heard of a botnet, it's likely because they go largely undetected.What they are:
A collection of software robots, or 'bots', that creates an army of infected computers (known as ‘zombies') that are remotely controlled by the originator. Yours may be one of them and you may not even know it.What they can do:
- Send spam emails with viruses attached.
- Spread all types of malware.
- Can use your computer as part of a denial of service attack against other systems.

Distributed denial-of-service (DDoS) attack
What it is:
A distributed denial-of-service (DDoS) attack — or DDoS attack — is when a malicious user gets a network of zombie computers to sabotage a specific website or server. The attack happens when the malicious user tells all the zombie computers to contact a specific website or server over and over again. That increase in the volume of traffic overloads the website or server causing it to be slow for legitimate users, sometimes to the point that the website or server shuts down completely.It could be possible for malicious users to use your computer in one of these attacks. By taking advantage of security vulnerabilities or weaknesses, an attacker could take control of your computer. He or she could then force your computer to send huge amounts of data to a website or send spam to particular email addresses. The attacks are "distributed" because the attacker is using multiple computers, including yours, to launch the denial-of-service attacks.
What it can do:
The most common and obvious type of DDoS attack occurs when an attacker “floods” a network with useless information. When you type a URL into your browser, you are sending a request to that site's computer server to view the page. The server can only process a certain number of requests at once. If an attacker overloads the server with requests, it can't process yours. The flood of incoming messages to the target system essentially forces it to shut down, thereby denying access to legitimate users.What you can do:
There are steps you can take to reduce the likelihood that an attacker will use your computer to attack other computers:- Install and maintain anti-virus software.
- Install a firewall, and configure it to restrict traffic coming into and leaving your computer.
- Follow good security practices when it comes to maintaining your contact or email lists. Applying email filters may help you manage unwanted emails, by automatically processing incoming messages based on certain criteria that you set.
- Be cautious if you notice that your Internet connection is unusually slow or you can't access certain sites (and that your Internet connection is not down).
- Avoid opening email attachments, especially if they are from people you don't know.

Hacking
Hacking is a term used to describe actions taken by someone to gain unauthorized access to a computer. The availability of information online on the tools, techniques, and malware makes it easier for even non-technical people to undertake malicious activities.What it is:
The process by which cyber criminals gain access to your computer.What it can do:
- Find weaknesses (or pre-existing bugs) in your security settings and exploit them in order to access your information.
- Install a Trojan horse, providing a back door for hackers to enter and search for your information.

Malware
Malware is one of the more common ways to infiltrate or damage your computer.What it is:
Malicious software that infects your computer, such as computer viruses, worms, Trojan horses, spyware, and adware.What it can do:
- Intimidate you with scareware, which is usually a pop-up message that tells you your computer has a security problem or other false information.
- Reformat the hard drive of your computer causing you to lose all your information.
- Alter or delete files.
- Steal sensitive information.
- Send emails on your behalf.
- Take control of your computer and all the software running on it.

Pharming
Pharming is a common type of online fraud.What it is:
A means to point you to a malicious and illegitimate website by redirecting the legitimate URL. Even if the URL is entered correctly, it can still be redirected to a fake website.What it can do:
- Convince you that the site is real and legitimate by spoofing or looking almost identical to the actual site down to the smallest details. You may enter your personal information and unknowingly give it to someone with malicious intent.

Phishing
Phishing is used most often by cyber criminals because it's easy to execute and can produce the results they're looking for with very little effort.What it is:
Fake emails, text messages and websites created to look like they're from authentic companies. They're sent by criminals to steal personal and financial information from you. This is also known as “spoofing”.What it does:
- Trick you into giving them information by asking you to update, validate or confirm your account. It is often presented in a manner than seems official and intimidating, to encourage you to take action.
- Provides cyber criminals with your username and passwords so that they can access your accounts (your online bank account, shopping accounts, etc.) and steal your credit card numbers.

Ransomware
What it is:
Ransomware is a type of malware that restricts access to your computer or your files and displays a message that demands payment in order for the restriction to be removed. The two most common means of infection appear to be phishing emails that contain malicious attachments and website pop-up advertisements.What it can do:
There are two common types of ransomware:- Lockscreen ransomware: displays an image that prevents you from accessing your computer
- Encryption ransomware: encrypts files on your system's hard drive and sometimes on shared network drives, USB drives, external hard drives, and even some cloud storage drives, preventing you from opening them
What you can do:
Do not pay the ransom. These threats are meant to scare and intimidate you, and they do not come from a law enforcement agency. Even if you submit payment, there is no guarantee that you will regain access to your system.If your computer has been infected (i.e. you are unable to access your computer or your files have been encrypted), contact a reputable computer technician or specialist to find out whether your computer can be repaired and your data retrieved.
In order to lessen the impact of a ransomware infection, be sure to regularly back-up your data with a removable external storage drive. It's possible that your files might be irretrievable; having an up-to-date backup could be invaluable.
In order to report the incident, please contact your local police and the Canadian Anti-Fraud Centre at 1-888-495-8501 or http://www.antifraudcentre-centreantifraude.ca/
Learn more about protecting your computer.

Spam
Spam is one of the more common methods of both sending information out and collecting it from unsuspecting people. Canada has a new anti-spam legislation that you can learn more about at www.fightspam.gc.caWhat it is:
- The mass distribution of unsolicited messages, advertising or pornography to addresses which can be easily found on the Internet through things like social networking sites, company websites and personal blogs.
- Canada's anti-spam legislation applies to all commercial electronic messages. A commercial electronic message is any electronic message that encourages participation in a commercial activity, regardless of whether there is an expectation of profit.
What it can do:
- Annoy you with unwanted junk mail.
- Create a burden for communications service providers and businesses to filter electronic messages.
- Phish for your information by tricking you into following links or entering details with too-good-to-be-true offers and promotions.
- Provide a vehicle for malware, scams, fraud and threats to your privacy.

Spoofing
This technique is often used in conjunction with phishing in an attempt to steal your information.What it is:
A website or email address that is created to look like it comes from a legitimate source. An email address may even include your own name, or the name of someone you know, making it difficult to discern whether or not the sender is real.What it does:
- Spends spam using your email address, or a variation of your email address, to your contact list.
- Recreates websites that closely resemble the authentic site. This could be a financial institution or other site that requires login or other personal information.

Spyware
Spyware & Adware
Spyware and adware are often used by third parties to infiltrate your computer.What it is:
Software that collects personal information about you without you knowing. They often come in the form of a ‘free' download and are installed automatically with or without your consent. These are difficult to remove and can infect your computer with viruses.What it can do:
- Collect information about you without you knowing about it and give it to third parties.
- Send your usernames, passwords, surfing habits, list of applications you've downloaded, settings, and even the version of your operating system to third parties.
- Change the way your computer runs without your knowledge.
- Take you to unwanted sites or inundate you with uncontrollable pop-up ads.

Trojan Horses
A Trojan horse may not be a term you're familiar with, but there's a good chance you or someone you know has been affected by one.What it is:
A malicious program that is disguised as, or embedded within, legitimate software. It is an executable file that will install itself and run automatically once it's downloaded.What it can do:
- Delete your files.
- Use your computer to hack other computers.
- Watch you through your web cam.
- Log your keystrokes (such as a credit card number you entered in an online purchase).
- Record usernames, passwords and other personal information.

Viruses
Most people have heard of computer viruses, but not many know exactly what they are or what they do.What they are:
Malicious computer programs that are often sent as an email attachment or a download with the intent of infecting your computer, as well as the computers of everyone in your contact list. Just visiting a site can start an automatic download of a virus.What they can do:
- Send spam.
- Provide criminals with access to your computer and contact lists.
- Scan and find personal information like passwords on your computer.
- Hijack your web browser.
- Disable your security settings.
- Display unwanted ads.
How will you know if your computer is infected?
Here are a few things to check for:- It takes longer than usual for your computer to start up, it restarts on its own or doesn't start up at all.
- It takes a long time to launch a program.
- Files and data have disappeared.
- Your system and programs crash constantly.
- The homepage you set on your web browser is different (note that this could be caused by Adware that has been installed on your computer).
- Web pages are slow to load.
- Your computer screen looks distorted.
- Programs are running without your control.

Wi-Fi Eavesdropping
WiFi eavesdropping is another method used by cyber criminals to capture personal information.What it is:
Virtual “listening in” on information that's shared over an unsecure (not encrypted) WiFi network.What it can do:
- Potentially access your computer with the right equipment.
- Steal your personal information including logins and passwords.

Worms
Worms are a common threat to computers and the Internet as a whole.What they are:
A worm, unlike a virus, goes to work on its own without attaching itself to files or programs. It lives in your computer memory, doesn't damage or alter the hard drive and propagates by sending itself to other computers in a network – whether within a company or the Internet itself.What they can do:
- Spread to everyone in your contact list.
- Cause a tremendous amount of damage by shutting down parts of the Internet, wreaking havoc on an internal network and costing companies enormous amounts of lost revenue
== INFECTION WORMS MA THE CONSIST DELETED EL ECTRON IC PROG MATIC ==
It is a great post on computer worm. Please read another similar post: How computer worms spread?
BalasHapus